EU CRA, EU RED, & U.S. Cyber Trust Mark for IoT Manufacturers: A 90-day path to regulatory compliance readiness
The EU Cyber Resilience Act enforcement deadline is approaching. The U.S. Cyber Trust Mark is required by the end of the year to remain on federal procurement lists. Device manufacturers that have not begun compliance work are behind timelines required for product certification.The Regulatory Moment Has Arrived for IoT Manufacturers
For years, IoT device security was considered primarily a reputational risk to device manufacturers. Devices controlled and misused as botnets, CVEs that never got patched, devices shipping with default credentials — the consequences were real but diffuse. The liability sat with the victims of the attacks enabled by those devices, not with the manufacturers who shipped them.
That era is coming to an end. Three converging regulatory frameworks are changing the legal and commercial calculus for device manufacturers simultaneously:
The EU Cyber Resilience Act (CRA) establishes mandatory security requirements for products with digital elements sold in the European Union, including vulnerability handling processes, secure update mechanisms, Software Bill of Materials (SBOM), and incident reporting obligations. Vulnerability and incident reporting obligations begin September 11, 2026, with full enforcement starting December 11, 2027, including CE marking requirements. Non-compliance can result in market access withdrawal and significant financial penalties.
The EU Radio Equipment Directive (RED) delegated act, enforced via EN 18031, extends cybersecurity requirements to radio-connected products, which covers the vast majority of consumer IoT devices. Requirements include protection against network attacks, minimization of default credentials, and authenticated firmware updates.
The U.S. Cyber Trust Mark program, administered through the FCC with NIST IR 8425, creates a voluntary but commercially significant certification that enterprise buyers and major retailers are increasingly requiring from their IoT suppliers. “Voluntary” in the regulatory sense; effectively mandatory in the market access sense.
Together, these three frameworks cover most of the same technical ground. A well-structured 90-day compliance program can address all three simultaneously — if the sequence is right.
Why the Sequence Matters
Most device manufacturers approaching compliance for the first time make the same mistake: they treat it as a documentation exercise. They hire a consultant to produce a compliance gap report, commission a policy library, and schedule a certification audit. Six months later, they have beautiful documentation, yet their products remain vulnerable to cyber attacks.
The reason is that the hardest compliance requirements: secure over-the-air (OTA) update mechanisms, authenticated firmware signing, meaningful vulnerability triage, and incident response with regulatory notification timelines, are engineering and operational problems, not documentation problems. You cannot write your way to a functional OTA patch capability. You must build it.
The 90-day structure below sequences the work to address the engineering foundations first, the operational processes second, and the governance documentation third. It is also the sequence in which the regulatory requirements depend on one another: you cannot have a credible incident response process without knowing your attack surface, and you cannot produce an SBOM without code library inventory and dependency visibility.
Days 1–30: Align, Inventory, and Stabilize the Foundations
Regulatory Mapping and Executive Alignment
The first action is a structured mapping of the organization’s current product portfolio against the three regulatory frameworks. Not all products are equally affected: EU CRA scope is defined by whether a product has digital elements and network connectivity; EU RED applies to radio-connected devices; the US Cyber Trust Mark applies to any IoT product seeking U.S. market certification.
This mapping produces the organization’s prioritized compliance roadmap that highlights which products in each market face which deadlines, and establishes a shared understanding across engineering, product, legal, and executive leadership. The goal of this Day 1-30 executive alignment is a single approved risk posture: which products we are certifying first, what engineering resources are required, and what the commercial consequences of missing the timeline are.
Attack Surface and Asset Inventory
EU CRA Article 13 requires manufacturers to demonstrate knowledge of their own software components and attack surface, which is foundational to the next phases. The Day 1-30 inventory work covers:
Firmware component mapping and a code library dependency graph for each product family
Third-party component and open-source library inventory (SBOM foundation)
Network interface and protocol exposure per device category
Updated delivery infrastructure and current signing key management practices
Incident Response Baseline
EU CRA Article 14 requires manufacturers to notify ENISA (European Union Agency for Cybersecurity) of actively exploited vulnerabilities within 24 hours of discovery via their reporting platform (currently under development). EU RED requires updated notification processes. Similarly, the US Cyber Trust Mark requires documented incident disclosure. None of these requirements can be met without a tested incident response process.
The Day 1-30 deliverable is an incident response playbook tailored to IoT-specific scenarios: firmware vulnerability exploitation, supply chain compromise, OTA update integrity failure. Along with a tabletop exercise that validates the “who decides, in what timeframe, and who gets notified” chain. The 24-hour ENISA notification window is unforgiving. Organizations that have not rehearsed it will miss it.
Days 31–60: Build the Technical Compliance Stack
Firmware Signing and Authenticated Update Infrastructure
This is the core technical deliverable of the compliance program and the requirement that most device manufacturers are furthest from meeting. EU CRA Article 13 requires secure update mechanisms. EN 18031-1 §6.3 [SUM-1, SUM-2] requires authenticated, integrity-verified firmware updates (the harmonized standard under RED Art. 3(3)(d), effective August 1, 2025). The US Cyber Trust Mark (NIST IR 8425 software update capability) requires verified firmware update baselines.
Meeting these requirements in a way that scales across a product portfolio with multiple hardware revisions, multiple regional deployments, and a device fleet already in the field requires an automated firmware signing and OTA delivery infrastructure. Manual firmware signing processes do not scale to the update cadence required for ongoing compliance.
Immutaverse’s platform handles the cryptographic signing, key management, and OTA delivery pipeline. The Day 31-60 work integrates this infrastructure into the manufacturer’s existing build and release workflow and validates it against the first wave of priority products.
SBOM Generation and Dependency Visibility
EU CRA Article 13 requires a Software Bill of Materials. The requirement is not a one-time deliverable. It is an ongoing obligation that must be maintained and updated as software components change. The Day 31-60 work establishes SBOM generation as part of the firmware build process, integrated with the vulnerability intelligence layer to automatically flag newly disclosed CVEs that affect components in the SBOM.
Vulnerability Management Operating Model
EU CRA Article 14 establishes coordinated vulnerability disclosure requirements. EU RED and the US Cyber Trust Mark both require documented processes for handling vulnerability reports. The Day 31-60 work establishes:
Public responsible disclosure intake with documented SLA (maximum exposure window before patch release)
Internal vulnerability triage processes using EPSS and real-world threat context (not just CVSS scores) to prioritize fixes
Integration with Immutaverse’s AI prioritization layer to automatically queue high-risk vulnerabilities for agentic patch generation
Days 61–90: Governance, Documentation, and Certification Readiness
Compliance Documentation Package
With the technical foundations in place, Days 61-90 produce the documentation required for certification assessment: technical file for CRA CE marking, EN 18031 conformance evidence for RED, and the NIST IR 8425 alignment documentation for Cyber Trust Mark. These documents are credible only because they describe real technical controls — not aspirational policies — and are supported by the audit trails the Immutaverse platform generates automatically.
Executive and Board Reporting
The Day 61-90 deliverable for leadership is a compliance posture dashboard and a 12-18-month roadmap covering which products achieve certification by which date, the ongoing engineering investment required, and how the compliance program maps to commercial requirements from major buyers and retail partners. This document answers the board’s question about regulatory exposure.
Operational Drills and Ongoing Readiness
A second incident response exercise, focused specifically on the regulatory notification scenarios, includes a CRA Article 14 notification drill with the 24-hour ENISA window, a coordinated disclosure scenario with an external researcher, and an OTA update integrity failure scenario. The goal is a team that can execute regulatory obligations under pressure, not just one that has read the policy.
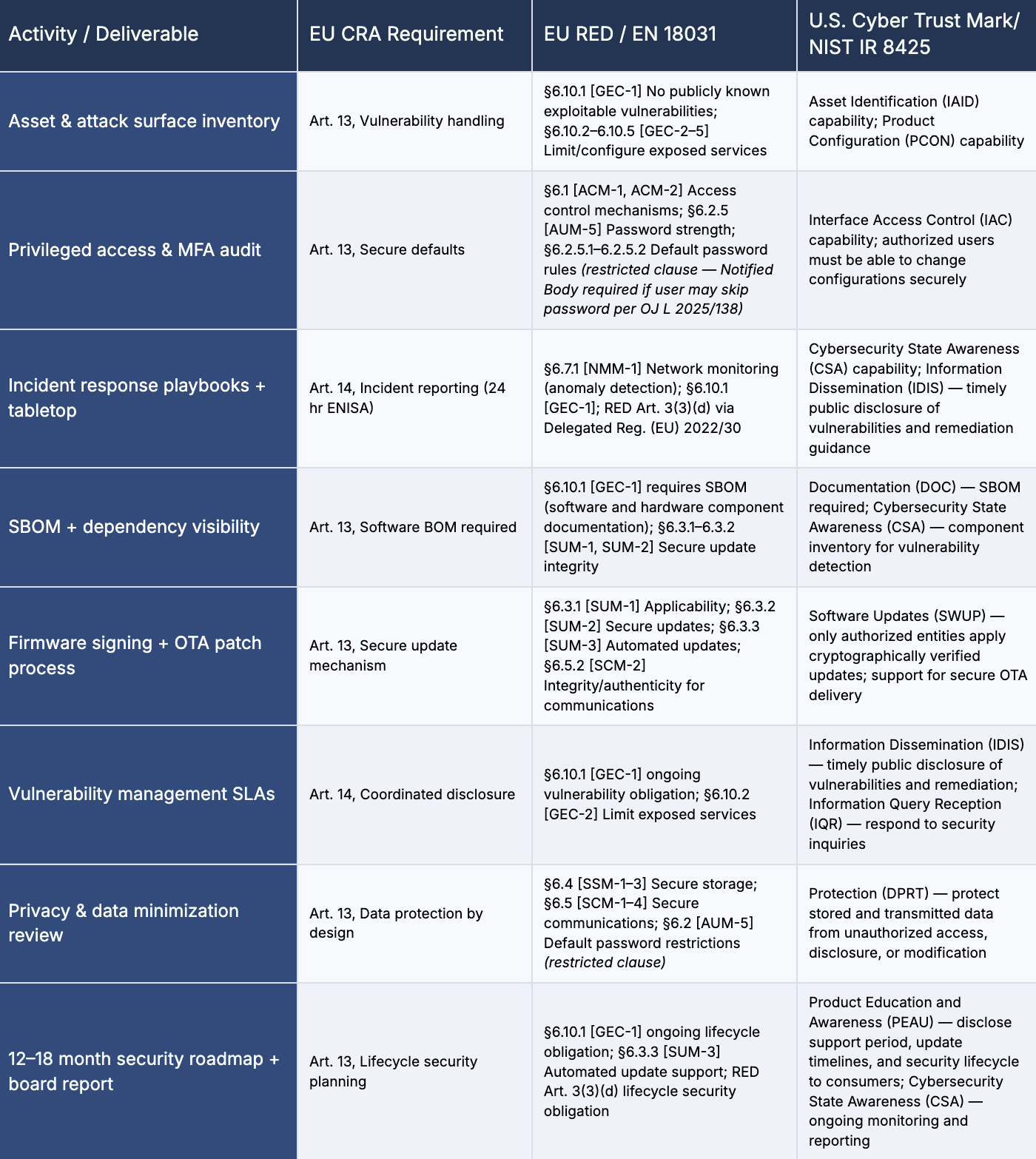
Regulatory Requirement Mapping
This table links each activity in the 90-day program to the specific requirements of CRA, RED / EN 18031, and the U.S. Cyber Trust Mark. This mapping serves as the compliance evidence framework, and every deliverable can be traced back to the regulatory requirement it addresses.
Compliance activities and deliverables across EU CRA, EU RED, and the US Cyber Trust Mark.
How Immutaverse Helps Manufacturers Meet Compliance Deadlines
The platform we have built at Immutaverse was designed specifically for the compliance challenges IoT device manufacturers face. Our agentic AI platform automates the most technically complex and time-consuming parts of the compliance journey:
Automated firmware signing and cryptographic verification, eliminating the bespoke workflows that consume engineering team bandwidth and introduce human error into the update integrity chain
AI-driven vulnerability prioritization using EPSS, CVSS, and real-world threat activity data, so engineering teams are fixing the vulnerabilities most likely to be exploited under EU CRA Article 14 coordinated disclosure timelines, not just the highest-severity scores
SBOM generation and code library dependency visibility integrated into the firmware build process, addressing EU CRA Article 13 SBOM requirements without adding manual tracking overhead
OTA orchestration with full audit trails, providing the documented update history that certification assessors and regulators require
The 90-day plan above reflects what is achievable when Immutaverse’s platform manages the automated components along with a structured engagement that focuses human effort on the organizational and process dimensions technology cannot replace.
The Commercial Case for Moving Now
Compliance timelines create a first-mover dynamic in regulated markets. The device manufacturers that achieve CRA certification earliest will have a documented competitive advantage in European procurement — particularly in B2B and public sector channels where regulatory compliance is a procurement gate, not just a preference.
In the U.S., the Cyber Trust Mark is following the same adoption curve as Energy Star: voluntary in the regulatory sense, yet effectively mandatory as major retailers and enterprise buyers begin requiring it from IoT suppliers. The manufacturers that build the compliance infrastructure now will be able to certify new products significantly faster than competitors starting from scratch.
Manufacturers that wait until enforcement actions create urgency will face a more expensive, more disruptive compliance journey and will spend that time at a commercial disadvantage relative to competitors who moved earlier.
Compliance is a one-time investment in infrastructure that pays dividends across every product’s security for life. This 90-day structure is designed to make that investment as efficient as possible.
Need help identifying required compliance tasks for your products?
Get a compliance readiness assessment for EU CRA, EU RED, and the US Cyber Trust Mark for $449.